How do you enable remote and hybrid users to work securely and productively?
Many technologies are available to support remote and hybrid working. However, businesses often struggle to identify which is best for their needs. From performance to security to cost, there are many considerations—and often, the chosen solution creates more headaches than it solves. This article compares two common technologies—VDI vs. VPN—notes their differences and challenges, and suggests a path to help businesses enable and secure their digital hybrid workforces.
VDI vs. VPN: What’s the Difference?
Virtual Private Networks (VPNs) and Virtual Desktop Infrastructure (VDI) are two of the most commonly used secure remote access solutions—technologies used by businesses to enable remote and hybrid workforces to work productively from anywhere. With that said, the question of VPN vs. VDI is arguably the wrong one. These technologies aren’t direct replacements for each other—they serve different (albeit related) purposes.
In simple terms, a VPN is a secure “tunnel” for communications between a remote device and a business server, while VDI provides self-contained virtual desktop environments for remote users. The two technologies are frequently used together to provide users with secure remote connectivity to business networks and applications.
To help you understand why, we’ll dive a little deeper into what a VPN is and how they work.
How Does a VPN Work?
A typical remote access VPN has two elements:
- A Network Access Server (NAS) – connected to the destination network or resource. This can be a dedicated on-site server or a software application installed on a shared or cloud server.
- A VPN software client – is installed on each remote device.
End users simply turn on their VPN client, which establishes an encrypted connection to the desired business network or resource. This connection is often likened to a “tunnel,” inside which traffic is encrypted and secured against interception.
Speed and Security Challenges for VPN and VDI Solutions
There are a number of potential challenges that any VPN technology must face, including:
- Latency (particularly for cloud-hosted VPNs).
- Maintenance cost and effort.
- Complexities when accessing cloud-hosted applications.
- Reliance on end-user devices for computing resources (a particular problem for BYOD).
However, perhaps the biggest issue with using a VPN alone as a remote access solution is security.
A VPN ensures secure communications between a remote device and an IT resource. Any data transferred between those endpoints is encrypted, but once it arrives, the onus of security is transferred to the endpoint.
This is generally not a problem on the business end, as there should be adequate security controls in place. However, there is no guarantee that sensitive data will be secure once it reaches a remote device. This is especially problematic if the remote device is a user’s personal laptop or smartphone, as there is no way to be certain a device has not already been compromised. Note that these security challenges apply if a VPN is used in isolation. Many businesses use VPNs in combination with other technologies to enable more secure remote access. This is where VDI comes in.
VDI Challenges
While it may seem an ideal remote workforce solution—since it allows businesses to enforce security and operational controls at all times—VDIs present several challenges.
Some of the most prevalent VDI challenges include:
- Complexity. For a VDI to function effectively, administrators must continuously maintain the servers, hypervisors, storage, networks, software, and desktop images involved. That’s a lot of software and hardware to maintain, and it requires significant time and expertise. Security is also far from simple, requiring input, time, and expertise from another set of stakeholders.
- Performance. This is perhaps the #1 frustration for businesses that rely on VDI. Today’s VDI solutions have improved significantly, but performance remains an issue. While each environment is virtual, the servers that host them are real and require regular maintenance, upgrades, and replacement. Since hardware is limited, it’s common for users to be frustrated by poor performance, particularly during peak times.
- Cost. Beyond the costs of set up, operation, and maintenance, VDI implementations are a constant balance between cost and performance. If a business grows or suddenly sees an increase in the need for remote working, it’s likely additional CAPEX spend will be needed to ensure sufficient hardware resources are available to protect performance and availability.
It’s Not (Necessarily) One or the Other
As we’ve seen, VDI vs. VPN is the wrong question because they perform different functions. VDI implementations often use a VPN to secure traffic between remote users and VDEs. After all, failing to secure this traffic would present a threat to security and privacy, and place businesses at risk of non-compliance fines from regulatory authorities. Still, while a well-executed implementation of this approach can be very secure, the challenges associated with both VPNs and VDIs remain. Fortunately, there is another way.
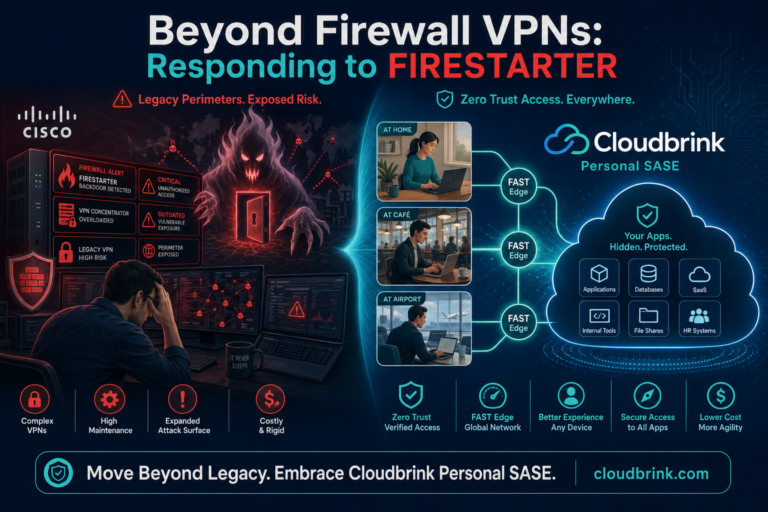
VPN and The High-Performance Distributed Workforce
Enabling users to stay productive while working remotely is paramount. However, many businesses continue to rely on a blend of VPNs and VDIs, despite poor performance, complexity, and high costs.
Cloudbrink provides secure, high-performance networking for the distributed hybrid workforce. Our software-only, high-performance ZTNA with personal SD-WAN and Moving Target Defense provides a host of benefits, including:
- Significantly improves remote employee productivity.
- Delivers up to a 30X increase in network and application performance.
- Reduces IT remote access support tickets and increases staff morale.
- Faster performance for cloud, SaaS, and data center applications.
- Reduces operational complexity for network, security, and IT administrators.
To give your users an in-office experience from anywhere—and remove serious IT and operational headaches—get your FREE VPN Replacement Demo today.