Cybercriminals looking to bypass defenses are persistent and will put in the time needed to probe the publicly facing systems they attack. Attackers invest time to build a picture of the IT systems and the defensive solutions in place. They will also aim to create profiles for people in the targeted organizations via social engineering techniques to use later for Phishing and other attacks.
Cybersecurity professionals understand this and have been changing the attack surface presented to the world on a regular basis to disrupt the reconnaissance and mapping activities of attackers. The goal is to prevent them from building a comprehensive picture of the IT systems and defenses they can use to plan an attack.
This technique of periodically changing the defensive landscape is called Moving Target Defense (MTD). Manually doing this is resource intensive and prone to errors that can weaken security or disrupt service delivery. There are also questions about how effectively it disrupts attack planning if the defensive surfaces aren’t changing rapidly enough.
Automated Moving Target Defense and VPN Alternatives
Automated Moving Target Defense (AMTD) is a newly emerging way to deliver MTD in a way that builds on the provable benefits of the technique while eliminating the issues of doing it manually. As you’ve probably guessed, the change in AMTD is to automate the variations within IT systems and defensive solutions. AMTD exploits the principle that a moving target presents a more formidable challenge for attackers than a stationary one. It employs tactics that involve orchestrating and automating changes in various systems and layers of an IT environment to increase uncertainty and complexity within the targeted systems.
AMTD uses four core pillars:
- Proactive cyber defense mechanisms
- Automation to orchestrate movement or change in the attack surface
- The use of deception technologies
- The ability to execute intelligent (preplanned) change decisions
In general, AMTD helps to decrease the areas vulnerable to attacks by implementing strategic modifications. It also increases the effort that cybercriminals need to use to plan attacks. Essentially, it normalizes the altering, concealing, or transforming of different parts of attack surfaces to disrupt attacker planning activities.
The term AMTD comes from Gartner, and it is outlined and described in an emerging technology discussion paper they published in February 2023. Search Gartner Automated Moving Target Defense to read more and find links to the paper (available to Gartner subscribers), or sign up for an upcoming Gartner webinar on this topic.
According to Gartner predictions, by 2025 a quarter of cloud applications will incorporate AMTD features and concepts to reinforce existing Cloud Web Application and API Protection technologies. In addition, they say that by 2025 AMTD-based solutions will replace at least 15% of traditional solutions that focus on detection and response.
They also expect that by 2030, AMTD-based hardware and software solutions resistant to exploitation will appear. This will shift the focus of security measures towards preventing identity misuse, social engineering defenses, and securing business processes rather than focusing solely on endpoint, application, and workload security strategies.
Cloudbrink Support for MTD
Cloudbrink’s Hybrid Access-as-a-Service (HAaaS) has automated features within the high-performance Zero Trust Network Access (ZTNA) component that enables AMTD as follows:
Rotating Certificates – Cloudbrink aids AMTD delivery by enabling the rotation of security certificates every 8 hours or less. This constant change in authentication certificates for user connections makes it challenging for attackers to intercept and decode traffic as part of their reconnaissance and planning activities.
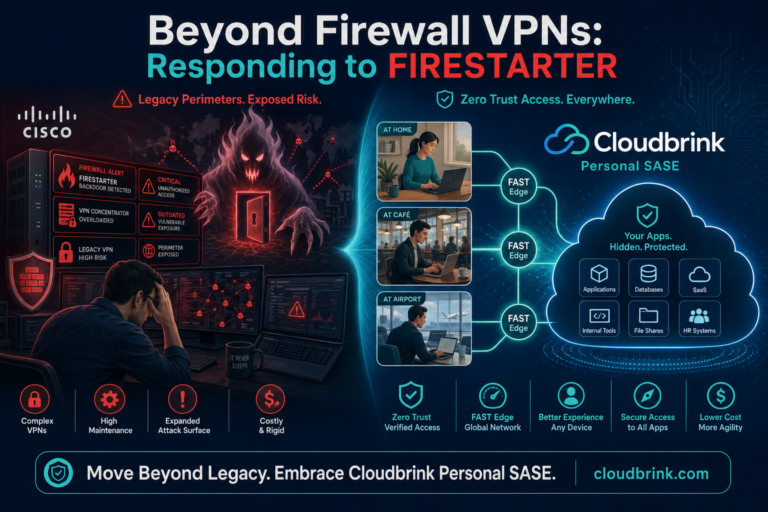
Temporary PoPs – Cloudbrink uses a dynamic network structure consisting of numerous flexible, autonomous, smart, and temporary Points of Presence (POPs) known as FAST Edges. These FAST Edges are temporary as they only exist while users connect to the network. As a result, attackers have no fixed location to target, making it challenging to surveil and analyze the network.
Conclusion
The concept of AMTD in cybersecurity is both innovative and effective as it aims to establish a secure environment that is constantly changing and, therefore unpredictable.
Today, ZTNA , VPN, SDP, and SD-WAN remote access solutions use fixed PoPs with IP addresses that rarely – if ever – change and they typically rotate certificates over months or years (Cisco 10-year certificate problems). This gives the attackers a lot of time to find a weakness.
Cloudbrink’s temporary Points of Presence and rapidly changing security certificates deliver AMTD concepts to disrupt attackers without burdening IT teams or users. In fact, companies that have moved to the Cloudbrink service have benefitted from reduced operational costs and higher security.