Automated Moving Target Defense
The Future of Security
AMTD is essential in the age of AI generated attacks. It delivers proactive cybersecurity against the ever evolving threat landscape.

THE CHALLENGES
Everyone's attack surface is growing as as users access apps from unmanaged devices and unsecured networks.
Too many vendors, excessive hardware, and constant user complaints—does this sound like your organization?
In the shadowy corners of the digital realm, a nefarious phenomenon has emerged, revolutionizing the landscape of cybercrime. Cybercrime-as-a-Service (CaaS) is an organized crime model that provides threat actors with unprecedented access to tools, AI expertise, and services to wreak havoc.
Despite massively expanding investment in cybersecurity, damage from cyberattacks continues to rise at an unprecedented rate, projected to reach over $10 trillion by 2025.
Attackers are using AI large language models to create smarter malware
ZTNA 2.0, SDP, and VPN architecture use fixed PoPs providing attackers with static sites that they can investigate for attacks.
Security Certificates that last months or years give attackers plenty of time to explore and attack
Traffic takes the same path through the network via static PoPs
Millions of security alerts each day make it hard for Sec Ops teams to find the right needle in the needle stack!
ENTER AUTOMATED MOVING TARGET DEFENSE FOR ZTNA

WHAT IS AMTD?
MOVING POPS

SHORT LIFE CERTIFICATES

MULTIPLE PATHS | MULTIPLE CONNECTIONS
Cloudbrink provides a High-Performance ZTNA service using zero trust principles based on mTLS 1.3 and it delivers advanced Automated Moving Target Defense (MTD) by rotating security certificates, constantly moving PoPs, and changing network paths.
To avoid detection, modern attacks are "low and slow". By rotating certificates multiple times a day, these exploits that involve certificates are eliminated.
High Performance ZTNA, ZTNA and VPN Comparison
| Cloudbrink | ZTNA | VPN | |
|---|---|---|---|
| Branch user optimization | |||
| Hybrid user optimization | |||
| Multi-cloud connectivity | |||
| SaaS apps optimization | |||
| Software-only (minimal maintenance) | |||
| Single policy-definition (central control plane) | |||
| Single pane of glass visibility (aggregated visibility) | |||
| Granular control (per user per app) | |||
| SDP-compliant enterprise access | |||
| Automated Moving Target Defense |
A Secure and Performant Remote Access Solution
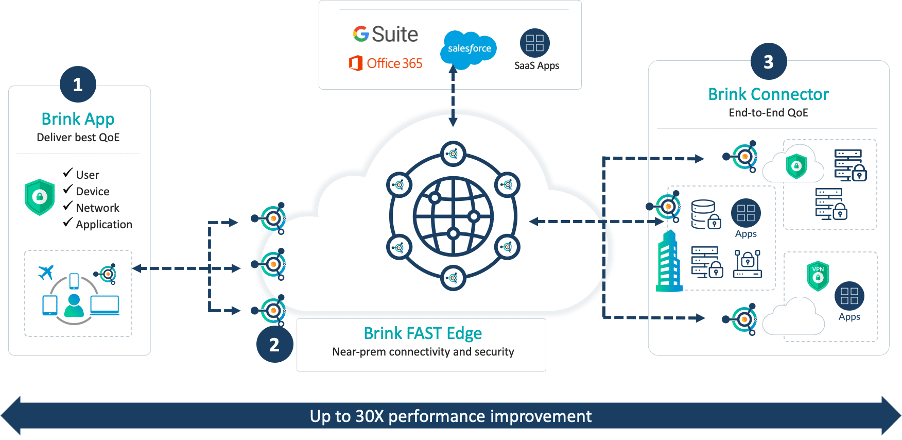
Cloudbrink's High-Performance ZTNA Three Main Components
The Brink App, installed on end-user devices, leverages the power of AI to overcome any network challenges and guarantees an excellent quality of experience for the end-user, regardless of the network.
Enterprise access points called FAST (Flexible, Autonomous, Smart, Temporary) Edges are automatically created close to the end user enabling Cloudbrink to react rapidly to changes in demand, guaranteeing the highest possible performance. Cloudbrink can automatically scale thousands of FAST Edges. By contrast, traditional vendors typically provide only 100-200 PoPs at most. These edges form a mesh to create the fastest possible route through the cloud on a per-session basis. In contrast, other ZTNA vendors typically provide only 100-200 PoPs at most.
If required, Cloudbrink's connector software can be deployed in the customer's cloud environment or data center to provide a secure end-to-end connection to private apps or data sources.
Cloudbrink's High-Performance ZTNA is a software-only solution that uses pre-emptive and accelerated packet recovery to minimize the impact of network issues. The zero trust network architecture with AMTD combines packet recovery with FAST edges to minimize latency.
Cloudbrink Zero Trust Architecture

“We were being pressured to go with Zscalar for the remote users, however the Cloudbrink zero trust access solution not only solved upgrading our current VPN environment but also improved our users' experience which is a win/win”.
SECURITY ARCHITECT
Financial Services
Financial Services