Gartner recently released several new reports in their Hype Cycle series, including a new Hype Cycle for Zero Trust Networking 2023. In this report, Gartner networking analysts discuss the technologies organizations use to deliver zero-trust strategies and programs. They do this while assuming, “By 2026, 10% of large enterprises will have a comprehensive, mature, and measurable zero trust program in place, up from less than 1% in 2023.”
What are Gartner Hype Cycles?
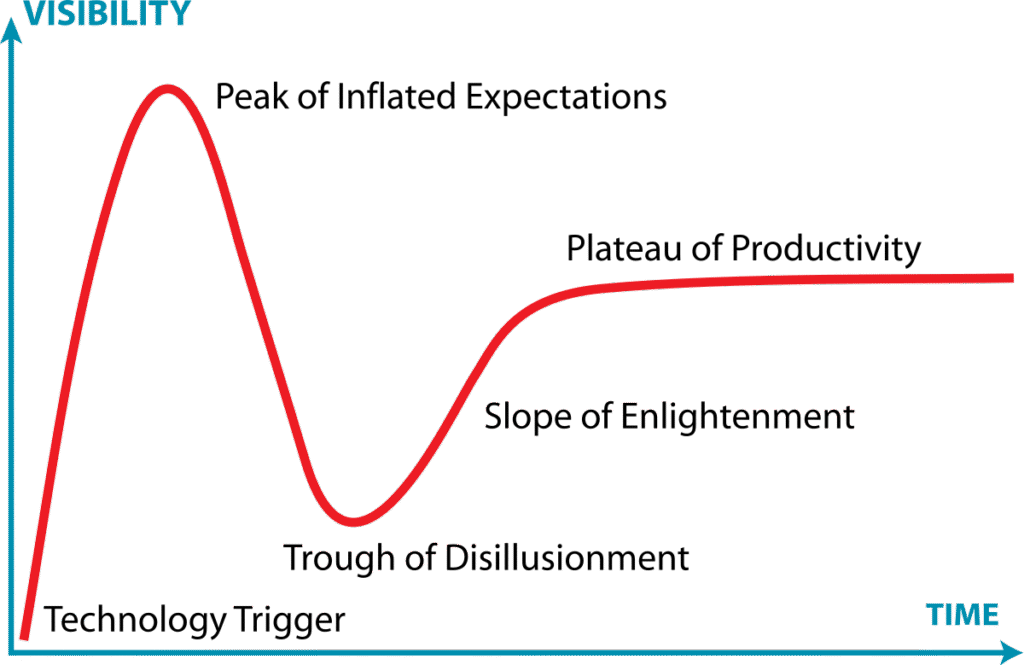
Gartner Hype Cycles offer a visual representation of a technology’s maturity and adoption and its potential to solve business problems and create opportunities. Each Gartner Hype Cycle helps business and technology leaders determine which new technologies are viable now, or soon will be, and which are still mainly hype without deliverable business benefits.
Each hype cycle charts technologies on a slope that has five key phases:
- Innovation Trigger – A technological breakthrough or a product launch that gets people talking.
- Peak of Inflated Expectations – Product or solution usage increases, and many success stories get reported (failures may not be). There is more hype than evidence that the innovation can deliver on the claims of those promoting it.
- Trough of Disillusionment – Initial interest wanes as over-hyped benefits that were claimed fail to materialize.
- Slope of Enlightenment – Genuine successes emerge as practical applications and benefits become clearer. Information on how the new technology can benefit businesses becomes available. Additional products appear from technology providers, and more adoption occurs.
- Plateau of Productivity – The new technology becomes routine, and mainstream adoption takes off. Criteria for assessing provider viability are more clearly defined.
Rational behind the Gartner Zero Trust Hype Cycle
Zero trust has become a mantra for those looking to reduce cyber risk in businesses and other organizations from a vendor, service provider, or business decision-maker perspective. At its core, zero trust replaces the traditional security model that assumes everything inside the corporate network can be trusted and everything outside the network is dangerous. In contrast, zero trust assumes that no user or device can be trusted by default, regardless of location or context.
Zero trust requires strict identity verification, access controls, and continuous monitoring and analytics to ensure that users and devices get authenticated and authorized before they can access resources. This approach helps protect against insider threats, external attacks, and data breaches by limiting access to only what is needed for any task. Zero trust also enables secure access for remote workers, contractors, and third-party vendors without compromising security.
Delivering zero trust isn’t done by deploying a single product. Delivering it requires organizations to invest in people, processes and technologies to improve the zero trust posture of networking environments across multiple systems. There are many technology areas and solutions that can be employed to build and implement a zero trust strategy and program.
Technology Solutions Discussed in the Hype Cycle
The Gartner Zero Trust Hype Cycle includes discussions on 19 relevant technology areas used to deliver zero trust today. Technologies that will become more important as they progress through the five phases of the hype cycle chart. The technologies in each of the five phases are listed below. Those highlighted in bold text are further discussed below in the context of CloudBrink’s Hybrid Access as a Service (HAaaS) solution.
Innovation Trigger – Enterprise browsers, extranet-as-a-service, continuous access evaluation profile (CAEP), unified endpoint security, network assurance, managed secure access service edge (MSASE), Universal Zero trust network access (ZTNA), service connectivity layer, and hybrid mesh firewall platform.
Peak of Inflated Expectations – Security service edge (SSE), zero trust strategy, and Kubernetes networking.
Trough of Disillusionment – Digital experience monitoring and Secure Access Service Edge (SASE).
The slope of Enlightenment – Zero trust network access (ZTNA), openID connect, micro-segmentation, container security, and remote browser isolation.
Plateau of Productivity – None.
Cloudbrink Solutions to Boost Your Zero Trust Journey
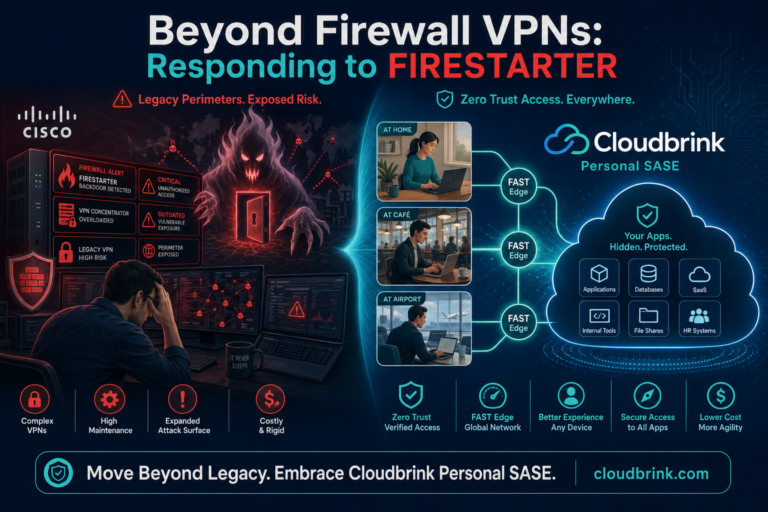
Cloudbrink exists to bring the fastest and most secure connectivity to end users, no matter where they are. Delivering this vision uses technologies across many of the 19 areas highlighted in Gartner’s Hype Cycle for Zero Trust Networking. By adopting Cloudbrink to deliver ZTNA (including universal ZTNA), SASE, and SD-WAN as core pillars in an SSE and zero trust strategy, business decision-makers, IT teams, and cybersecurity professionals can accelerate their zero-trust adoption without experiencing the disappointments others encounter in the Gartner Trough of Disillusionment.
Cloudbrink HAaaS delivers a fast and secure zero-trust experience for any hybrid workforce. It provides an experience for remote workers equivalent to that which in-office staff enjoy. Unlike traditional ZTNA and VPN solutions that sometimes compromise on security or degrade user performance, Cloudbrink’s service ensures user connections are secure, and it eliminates performance issues to deliver a fast, seamless, and productive end-user experience.
HAaaS is a software-only solution that delivers an optimal user experience by replacing legacy VPN and SD-WAN connectivity architectures with machine learning-based connectors that monitor local and regional connectivity across multiple cloud regions. Cloudbrink’s innovative technology dynamic points of presence, known as FAST edges, are located in Cloud data centers around the globe. This enables remote workers to experience a level of performance equivalent to working in the office, with an impressive 30x increase in application performance within a secure and zero trust-supporting solution. With simplified operations across the board, the enhanced end-user experience is also straightforward for network security teams and IT administrators to manage. Plus, it is invisible to end-users and provides them with a seamless experience.
Conclusion
Cloudbrink’s HAaaS solution offers zero trust security in a revolutionary way that changes the game for remote access. It empowers organizations with secure, reliable, and high-performance connectivity. Combining the agility and intelligence of ZTNA, SASE, and SD-WAN within HAaaS means organizations can overcome the limitations of traditional remote access solutions without compromising on access speeds or cybersecurity.
Cloudbrink HAaaS delivers a seamless user experience that enables IT teams to efficiently manage and secure their remote access infrastructure, whether it’s a remote workforce, branch offices, or multiple locations. As remote work continues to evolve, the deployment of Cloudbrink HAaaS will allow your staff to work effectively from anywhere, over whatever network connectivity is available.
References
- Gartner: Hype Cycle for Zero Trust Networking, 2023 – https://www.gartner.com/en/documents/4538899 (Gartner Account required for access)
- Gartner: Gartner Hype Cycle – https://www.gartner.com/en/research/methodologies/gartner-hype-cycle