FIRESTARTER Backdoor: Why Cisco Firewall Attacks Are a Wake-Up Call for Remote Access
CISA and the U.K. National Cyber Security Centre have released a Malware Analysis Report on FIRESTARTER, a persistent backdoor targeting publicly accessible Cisco Firepower and Secure Firewall devices running Cisco ASA or Firepower Threat Defense software. CISA also updated Emergency Directive 25-03, calling for action to identify and mitigate potential compromise of Cisco devices.
For security and infrastructure teams, the message is clear:
The remote-access edge has become one of the most attractive targets in the enterprise.
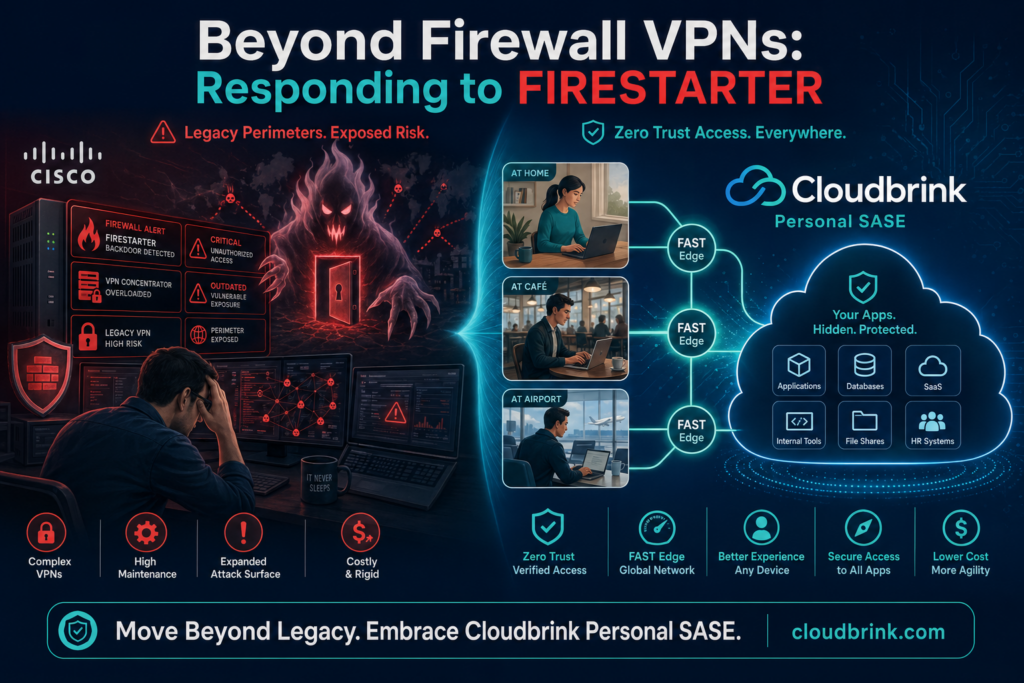
And while patching is essential, FIRESTARTER highlights a bigger strategic issue. Organizations that still depend heavily on internet-facing VPNs, firewalls, and perimeter appliances for remote access are carrying operational and security risk that modern hybrid work no longer requires.
In this article
What is FIRESTARTER?
FIRESTARTER is a backdoor associated with advanced persistent threat activity targeting Cisco Firepower and Secure Firewall devices. According to CISA, the malware enables remote access and control, and can maintain persistence even after firmware patching and device reboots.
Cisco Talos reports that the activity is linked to UAT-4356, which exploited CVE-2025-20333 and CVE-2025-20362 to gain unauthorized access to vulnerable Cisco Firepower devices and deploy FIRESTARTER.
That persistence matters. In many incidents, security teams assume that patching the vulnerable software closes the door. FIRESTARTER challenges that assumption because compromised devices may still require deeper hunting, forensic validation, reimaging, or replacement.
Why are Cisco ASA, Firepower, and Secure Firewall devices being targeted?
Attackers target remote-access infrastructure because it sits at the front door of the enterprise. VPN concentrators, firewalls, and secure access appliances often have direct internet exposure, privileged network placement, and trusted access into internal environments.
That makes them high-value targets.
When these devices are compromised, attackers may gain a durable foothold near the network perimeter. From there, they may attempt to maintain access, avoid detection, collect credentials, or pivot toward sensitive applications and data.
This is not just a Cisco issue. It is a legacy architecture issue.
Why patching alone is not a remote-access strategy
Patching remains mandatory. CISA, Cisco, and national cyber agencies are right to urge organizations to review advisories, investigate affected devices, apply mitigations, and report findings where required.
But FIRESTARTER shows why security leaders should ask a broader question:
Why are so many remote users still dependent on publicly exposed firewall and VPN infrastructure in the first place?
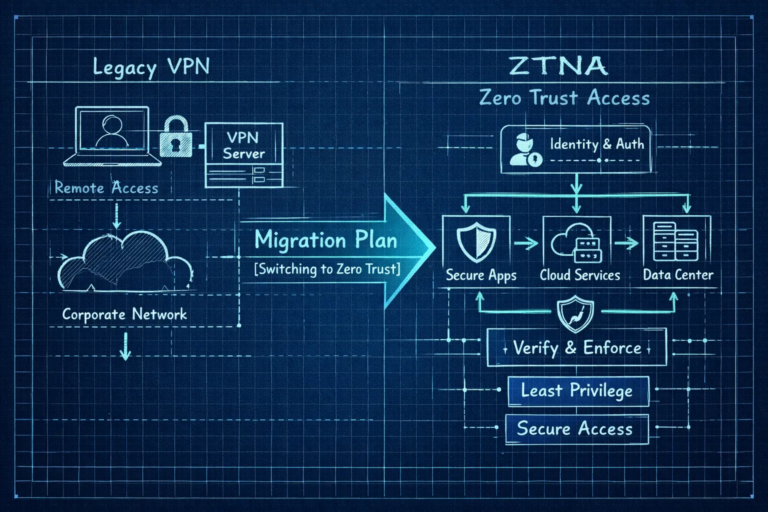
Traditional VPN and firewall-based remote access was designed for a different era, when most users were in offices, most applications lived in data centers, and remote access was the exception. Today, users are everywhere. Applications are spread across SaaS, private cloud, public cloud, and on-prem environments. The perimeter has dissolved, but many organizations still depend on perimeter-era tools.
That creates four problems:
1. More exposed infrastructure
VPN and firewall services must often be reachable from the internet. That exposure creates a target.
2. More patching pressure
Every urgent CVE becomes an operational fire drill.
3. More complexity
Multiple VPNs, firewalls, SD-WAN devices, and policy consoles create inconsistent access control.
4. Poor user experience
Hairpinning traffic through data centers slows down applications and increases support tickets.
The better question: how much Cisco firewall exposure can you remove?
Many enterprises cannot rip and replace every firewall overnight. Firewalls still have valid roles in data centers, branches, segmentation, and inspection. But remote access does not need to depend on the same architecture.
Cloudbrink™ Personal SASE helps organizations remove reliance on legacy VPNs and firewall-based remote access by shifting access closer to the user, enforcing zero trust, and delivering high-performance connectivity without requiring hardware appliances.
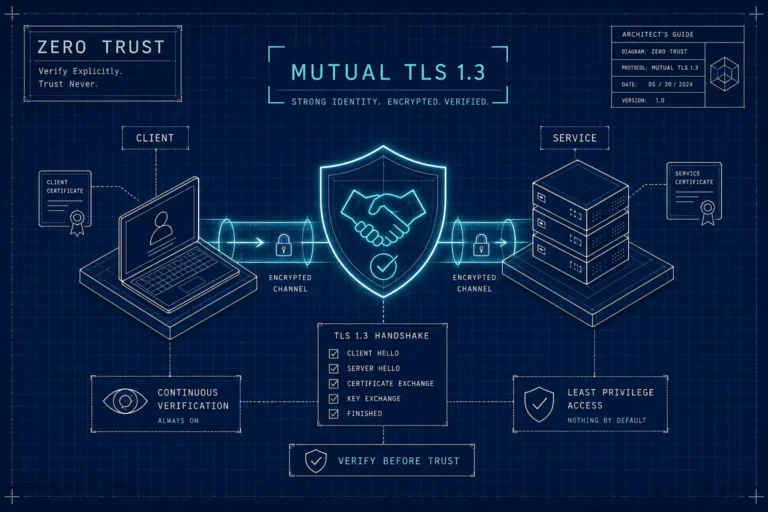
Cloudbrink’s software-only service includes the Brink App, FAST Edges, high-performance ZTNA, Safe AI, personal SD-WAN, Internet Security, and multi-cloud connectors. The platform uses Automated Moving Target Defense with mutual TLS 1.3, rotating certificates, least-privilege access, continuous device posture assessment, and Dark-Cloud secure access to keep private applications hidden from unauthorized users.
The result is simple: users get secure access to the applications they need, without forcing every remote session through legacy VPN concentrators or publicly exposed firewall access paths.
Real-world example: an insurance company moved away from Cisco and Fortinet VPNs
A leading U.S. insurance company had grown through acquisitions and was operating multiple VPN solutions, including Fortinet FortiClient and Cisco AnyConnect. As remote work expanded, the company faced performance bottlenecks, scalability challenges, security limitations, and high support overhead. Remote employees experienced slow, unstable access because traffic was being hairpinned through data centers.
The company evaluated alternatives, including Palo Alto Networks, Zscaler, Netskope, and VMware SD-WAN. The challenge was that other approaches still required traffic to be routed back through data centers for certain applications, reducing performance gains. Cloudbrink stood out because its single-tenant FAST Edge approach allowed direct, secure access to applications without the same hairpinning penalty.
The business impact was immediate:
The company transitioned 300 employees on Day 1 and more than 600 by the end of the first week. Remote connectivity support calls “pretty much disappeared” after moving away from Fortinet and Cisco VPNs. Employees in difficult connectivity locations, including Canada and Alaska, experienced seamless access to business applications. The company also began deploying Cloudbrink connectors in AWS and Azure to reduce dependency on on-prem data center infrastructure.
This is the practical path forward for many enterprises: not just patching the remote-access edge, but reducing dependence on it.
How Cloudbrink helps after advisories like FIRESTARTER
Cloudbrink is not a substitute for incident response. If you operate affected Cisco devices, follow CISA and Cisco guidance, hunt for compromise, preserve evidence where appropriate, and remediate impacted infrastructure.
But as security analyst company GigaOm note, Cloudbrink helps reduce the long-term risk that makes these incidents so disruptive.
Simplicity: fewer appliances, fewer access paths, fewer tickets
Cloudbrink is 100% software-only. There are no hardware gateways or uCPE devices to ship to remote users. Policies are managed centrally. Users connect through the Brink App, which automatically selects the optimal FAST Edge.
For IT teams, that means faster deployment and fewer moving parts. In the insurance case study, hundreds of users were migrated in days, and remote connectivity tickets largely disappeared after moving away from legacy VPN access.
Security: zero trust without exposing private applications
Cloudbrink uses mutual TLS 1.3, rotating device certificates, identity-based access, device posture checks, and least-privilege policies. Private applications are hidden using Dark-Cloud secure access principles, meaning unauthorized users cannot discover or connect to protected resources.
This reduces the attack surface compared with architectures that depend on publicly reachable VPN services and firewall-based entry points for remote workers.
Speed: secure access that users do not want to bypass
Security fails when users avoid it. Traditional VPNs often slow applications because traffic is backhauled through data centers or centralized gateways.
Cloudbrink’s FAST Edges are designed to sit close to users, while the Brink Protocol adapts to packet loss, latency, and unreliable last-mile networks. Cloudbrink’s product documentation describes FAST Edges as software-defined edges located within 5–20 ms of users, with a current worldwide average of 5.2 ms, and supporting up to 1 Gbps per user device.
When secure access feels fast, users stay protected.
FAQ: FIRESTARTER, Cisco firewalls, and VPN replacement
What devices does FIRESTARTER target?
FIRESTARTER targets publicly accessible Cisco Firepower and Secure Firewall devices running Adaptive Security Appliance or Firepower Threat Defense software, according to CISA.
Can FIRESTARTER survive patching?
Yes. CISA states that FIRESTARTER can maintain persistence after firmware patching and device reboots, which means compromised devices may require more than a standard patch cycle.
What vulnerabilities are associated with FIRESTARTER?
Cisco Talos reports that UAT-4356 exploited CVE-2025-20333 and CVE-2025-20362 to gain unauthorized access to vulnerable Cisco Firepower devices and deploy FIRESTARTER.
Should organizations still patch Cisco ASA, Firepower, and Secure Firewall devices?
Yes. Organizations should follow CISA and Cisco guidance, apply required updates, hunt for compromise, and report findings where appropriate. Patching is necessary, but FIRESTARTER shows that patching alone may not be sufficient if a device was already compromised.
Does Cloudbrink replace Cisco firewalls?
Cloudbrink replaces the need to rely on legacy VPN, NAC and firewall-based architectures for user access. Many organizations will still use firewalls for other network security functions, but Cloudbrink – using the Coffee-Shop-Networking for the enterprise model – can reduce the amount of user-access traffic and user dependency placed on Cisco firewall and NAC infrastructure.
Why move from VPN to Personal SASE?
Personal SASE gives hybrid workers secure, high-performance access from anywhere, without the complexity of traditional VPN, SD-WAN hardware, or multi-product SASE stacks. Cloudbrink combines ZTNA, personal SD-WAN, FAST Edges, Internet Security, and unified policy in a software-only service.
The takeaway: do not just patch the perimeter. Reduce your dependency on it.
FIRESTARTER is a timely reminder that internet-facing remote-access infrastructure is now a primary target. Security teams should absolutely follow CISA and Cisco guidance. But they should also use this moment to reassess the architecture itself.
The goal is not simply to survive the next emergency directive. The goal is to build a remote-access model that is simpler to operate, harder to attack, and faster for users.
Cloudbrink Personal SASE helps enterprises do exactly that: simplify access, strengthen security, and deliver the speed hybrid workers expect—while reducing reliance on legacy VPNs and firewall-based remote access.
Enjoy life and work
The New Office is Anywhere
Secure it without slowing it down.