Zero Trust has long been security’s most debated framework – powerful in principle, uneven in execution. As enterprises now confront the rise of autonomous AI agents, a critical question emerges: can Zero Trust evolve to meet this new challenge, or is its application to AI merely a rebranding exercise? The answer, clearly, is that Zero Trust remains the right framework – but only if vendors and enterprises commit to genuine, native implementation rather than surface-level adaptation.
The Core Principles Hold – But Implementation Must Change
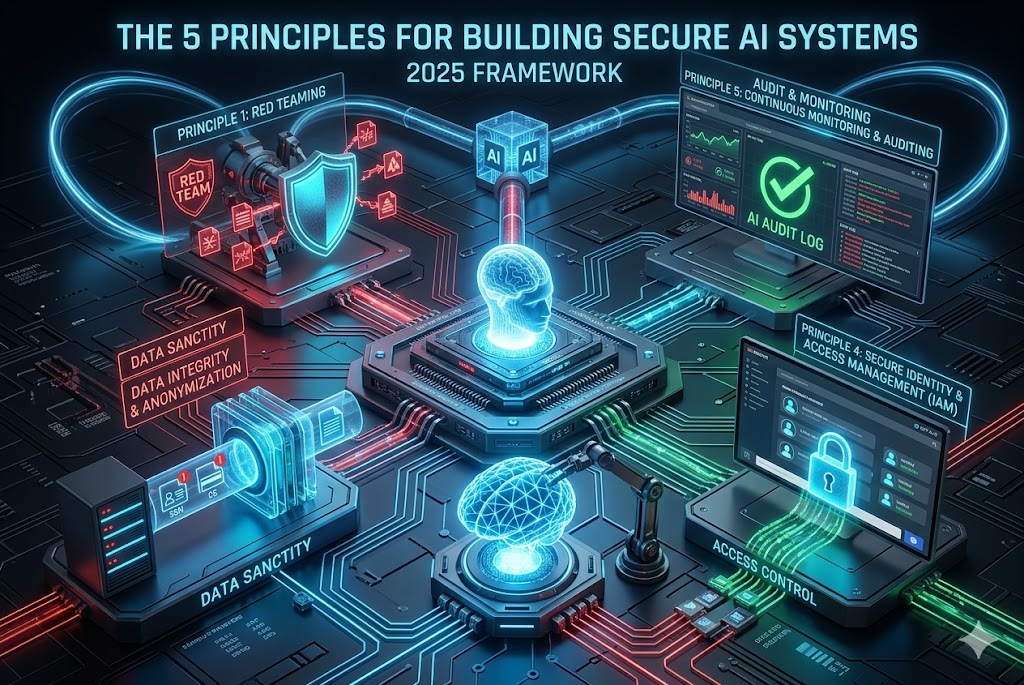
Zero Trust was not built for humans alone. Its foundational principles – authenticate and authorize every transaction, enforce role-based access controls, apply location-independent policy enforcement, and verify both user and endpoint trust – are equally applicable to AI agents. The principles do not need to be reinvented; the implementation layer does.
Where vendors and security teams must act is in rethinking how those principles are applied. Authenticating and authorizing an AI agent is a fundamentally different technical challenge from doing so for a human user. Access controls for agents must be context-aware, not merely role-based. Organizations that attempt to retrofit existing tools – for example, using URL filtering policies to identify AI agent traffic – are applying patchwork fixes to a structural problem. Native AI security guardrails, designed with AI ecosystems in mind, are not optional; they are mandatory.
The Attack Vectors Enterprises Are Not Ready For
AI introduces several attack vectors that most enterprise security stacks are currently blind to:
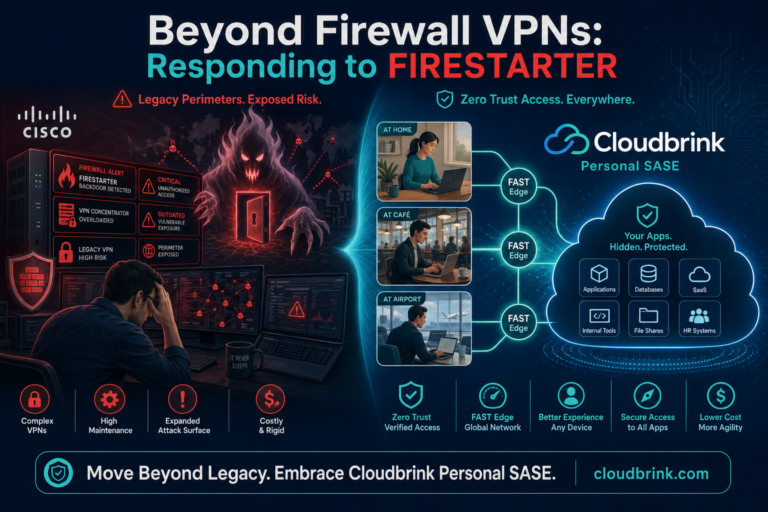
Shadow AI is the most immediate and widespread threat. Employees are adopting personal AI assistants and third-party AI services without IT approval, driven by the easy availability of these tools and the relative slowness of IT departments to define and communicate sanctioned alternatives. This ungoverned use creates significant exposure.
Unvetted AI Models compound the problem. The landscape of AI models – both general-purpose and domain-specific – is vast, and not all are adequately safeguarded. Legitimate users and malicious actors alike can exploit the same tools, enabling threats such as model manipulation and prompt injection.
Multi-Agent Workflows represent the frontier of enterprise AI risk. As organizations deploy chains of AI agents that pass decisions and actions between one another, the attack surface expands dramatically. Visibility, access controls, and monitoring across the full chain are essential – and largely absent from today’s security tooling.
Private AI Deployments introduce their own risks: ensuring that agents operating inside corporate networks have appropriately limited access to sensitive data, and that access can be revoked swiftly when necessary.
The Weakest Link Principle Applies – At Scale
In any multi-agent system, the security posture of the entire chain is determined by its least-secure component. A single compromised agent is not an isolated incident – it is a vector through which the integrity of the entire system can be undermined, producing corrupted decisions and undesirable outcomes that propagate without human review. This is not a marginal or theoretical risk. It is a structural vulnerability that enterprises must address before deploying AI agents at scale.
AI Governance Is a Process, Not a Checklist
Many enterprises are still in the early stages of AI governance, and it is tempting to treat this as a temporary gap that will close with time. It will not close on its own. AI governance is a multi-department, multi-function undertaking that requires changes to policies, processes, technology, and – most importantly – organizational mindset.
Meaningful AI governance demands dedicated investment: budget, personnel, and executive commitment. Teams across networking, information security, application development, and business leadership must align around a coherent AI strategy and the controls needed to execute it safely.
Zero Trust for AI Agents Protects the Organization – Survival Is at Stake
The security risk posed by AI agents is not incremental. It is potentially catastrophic. The same properties that make AI agents enormously productive – their autonomy, their speed, their ability to operate across systems and boundaries – make them extraordinarily dangerous if compromised or ungoverned.
Applying Zero Trust principles to AI agents is not about adding a compliance layer. It is about ensuring that organizations can realize the competitive and operational benefits of AI without assuming existential risk. The organizations that fail to implement proper AI security guardrails are not merely accepting a higher risk of breach; they are threatening their own continuity.
Accountability Is Shared – And Must Be Explicit
When an AI agent fails or is compromised inside a Zero Trust perimeter, accountability does not belong to a single team. It is distributed across the organization: networking teams responsible for access controls, information security teams for defining and enforcing safety guardrails, application teams for ensuring agents are scoped correctly and cannot move laterally, and management for overseeing AI adoption at the organizational level.
AI agents are not standalone applications. They are organization-wide transformations. Treating them as anything less – assigning responsibility to a single department, or treating AI security as a subset of existing IT operations – is a governance failure waiting to become a security failure.
Conclusion
Zero Trust for AI agents is not a superficial overlay or a mere rebranding of existing security tools. It is the essential framework for a new, transformative paradigm, demanding genuine, native implementation and purpose-built controls. Enterprises must reject the temptation of patchwork fixes and surface-level adaptation. Those organizations that take this challenge seriously—by investing in dedicated controls and establishing cross-functional governance structures—will be positioned to lead the market. Conversely, those that fail to commit to this level of diligence are accepting risks that extend far beyond reputation or compliance; they are threatening the organization’s very continuity and survival.