In the ever-evolving world of cybersecurity, vigilance is a non-negotiable. Today, the spotlight is on a serious vulnerability that demands immediate attention: CVE-2024-21762. This weakness is found in the heart of Fortinet’s FortiOS impacting SSL VPNs, and it is a gaping hole through which attackers could crawl to inflict damage on an unimaginable scale.
Fortinet devices are supposed to be renowned for their robust security features, yet ironically, they’ve been marked as a target by cyber adversaries, especially for those units with SSL VPN functionality activated. The CVE-2024-21762 vulnerability lets unauthenticated, remote hackers execute code arbitrarily – a form of cyber assault that can pose severe risks to private networks and guarded data.
The Threat Landscape
Imagine a scenario where malefactors gain unfettered access to your systems. Such infiltration can lead to data being pilfered, a sinister installation of ransomware, or a discreet reconnaissance of your network’s inner workings. Therefore, organizations leveraging Fortinet’s SSL VPN are the most affected since it attacks a fundamental aspect of their remote access capabilities.
The exploitability of CVE-2024-21762 cannot be understated. It underscored an urgent need for continued investment in dynamic defense measures, echoing the growing concern detailed in documents, for example, Cloudbrink’s web page on “Automated Moving Target Defense Security,” which prescribes rotational security certificates and proactive cybersecurity to counteract the threat of AI-generated offenses.
Combatting The Issue
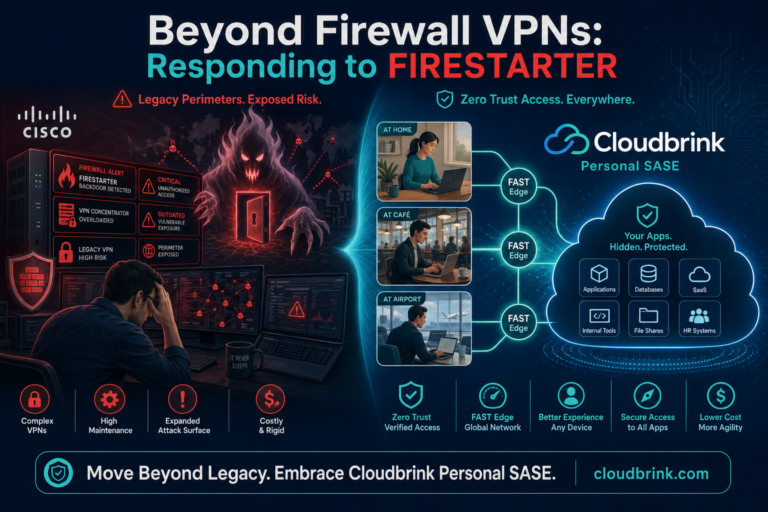
Even as organizations such as Cloudbrink present innovative solutions like Automated Moving Target Defense (AMTD), which employs strategies to make cyber targets less static and therefore harder to pin down, immediate measures must be taken to safeguard against this immediate threat by Fortinet.
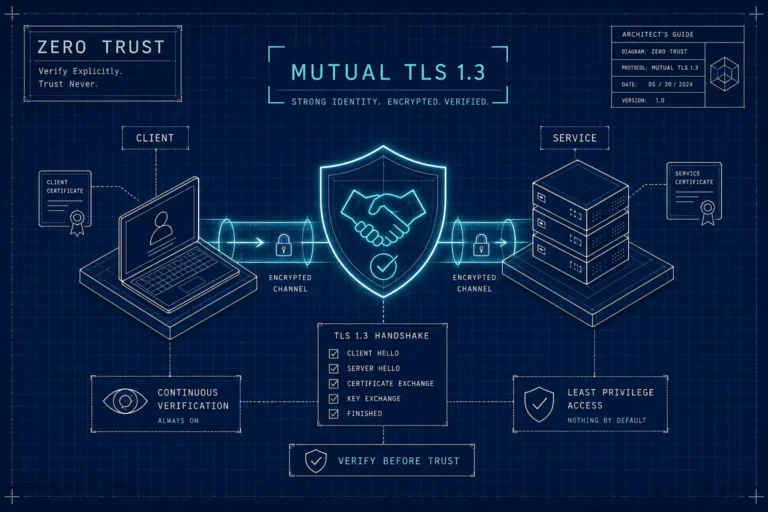
We urge users who currently cannot update to the latest patched versions to disable all SSL-VPN related devices promptly and consider switching to a cloud-based zero trust access service that uses mutual TLS 1.3 end to end. Assess your network for indicators that could signify a breach or attempted exploitation of this vulnerability.
Steps to Safety
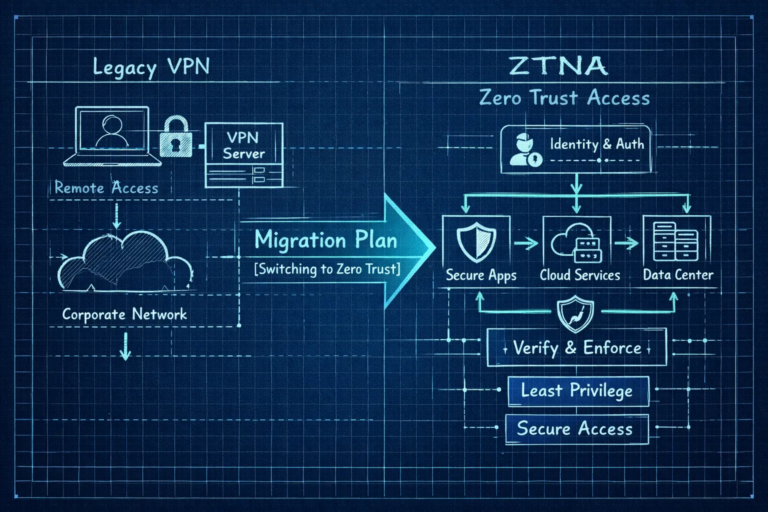
- Disable SSL-VPN: If you’re currently using an affected Fortinet device, and cannot immediately upgrade, consider disabling the SSL-VPN functionality to prevent unauthorized access attempts
- Monitor Networks: Consistently observe network traffic for anomalous behavior that could signal a compromise.
- Upgrade Promptly: Follow Fortinet’s guidance on updates and patches to ensure your systems are not susceptible to CVE-2024-21762.
- Consider Alternatives: In light of such vulnerabilities, exploring alternatives like Cloudbrink’s solutions that offer a novel approach to defense with FAST edges and Hi-Perf ZTNA could be a conversation worth having. Their personal SD-WAN and AMTD technology with constantly moving Points of Presence (PoPs) is in stark contrast to the static nature of VPN architectures that are easier targets for attackers.
- Educate Teams: Ensure that your cybersecurity teams are up to speed with the latest threats and are equipped to handle the complexities of today’s risks.
- Implement Zero Trust Principles: Utilize other security paradigms such as Zero Trust Architecture which, as described in the “Zero Trust and the Role of AMTD – Cloudbrink” document, assumes no implicit trust and continuously verifies every stage of digital interaction.
In conclusion, the threat posed by CVE-2024-21762 is significant, and complacency is not an option. As we steer through a landscape where cyber threats are increasingly sophisticated and automated, infrastructural agility becomes paramount. By considering both immediate and long-term defensive strategies, like the ones Cloudbrink offers, you can fortify your cybersecurity and protect your organization’s precious assets.